How Secure are Medical Devices?

As medicine continues to intersect the world of technology, doctors and patients have more capabilities than ever. Healthcare providers can more easily communicate with patients, sharing important images and information in a timely and efficient manner. The technological developments of medical devices have revolutionized the world of modern medicine – but it’s not all good.
And as more physicians use telemedicine and digitized medical devices, the likelihood of security risks increases. Cyberattacks and cloud misconfigurations are on the rise, and while every organization needs to protect its data, it is especially crucial in the medical industry. To ensure the protection of information in medical devices, we will discuss just how secure they are – and how you can improve security further.
Medical Device Security
First and foremost, it is essential to understand precisely what medical device security entails. The medical devices that a healthcare provider uses contain significant volumes of sensitive data, ranging from medical histories, personal patient information, and sensitive company data.
All of the data stored in a given medical device must be protected to ensure the integrity of a given healthcare provider. Medical device security refers to the practices and techniques used to prevent attacks against medical devices. Whether that refers to unauthorized access to a device or exposure of sensitive data, these attacks must be prevented.
As a healthcare provider, the integrity of you and your business depends on your ability to protect patient information. It is your responsibility to ensure the security of your medical devices, but it is not only you that is affected should a breach or attack occur. While instrumental in providing quality service, the medical devices you use come with security risks.
Fortunately, for this reason, there are several guidelines and requirements that must be followed to ensure the security of these devices. Even so, there are some additional practices you should implement to guarantee the protection of the information contained in your medical devices. As medical technology and telehealth services grow more popular, security is more important than ever.
Challenges
Before getting into how secure your devices are and how to improve upon them, it is vital to recognize the security challenges faced when using medical devices. There are four significant challenges that you will experience while handling medical device security:
- Handling sensitive data. Medical devices must be handled with much more care than the typical device as they contain highly sensitive personal information. The information you are protecting can directly impact your patients should it be compromised. For this reason, ensuring security will be an utmost priority for your business.
- Compliance. As your medical devices will be handling such sensitive data, there are numerous laws and regulations you must abide by to remain in compliance. Following these requirements is critical to maintaining the integrity of your organization while avoiding fines and legal repercussions.
- Cyberattacks. Another significant challenge, and perhaps the most daunting, is the risk of cyberattacks. While most regulations will help you avoid breaches and attacks, you could still likely face one. Because medical devices are often mass-produced, once an entry point for a breach is discovered, it is easy to replicate – thus increasing the likelihood of a breach. Additionally, because devices can be accessed from external networks, there are more opportunities for attacks.
- Lifecycle. In addition to being mass-produced, medical devices are also designed for lifecycles for as long as 20 years. For this reason, devices are not always compatible with updates, potentially leaving them outdated, inefficient, and susceptible to breaches. For this reason, it is vital to choose your device carefully.
Security Requirements
As mentioned, there are numerous guidelines that healthcare providers should adhere to concerning medical devices. As these devices contain such sensitive patient information, the FDA has issued several recommendations for providers to remain in compliance. The most prominent of these guidelines include:
- Restriction of unauthorized access to medical devices.
- Ensure firewalls are maintained and up to date.
- Monitor network activity for irregular or unauthorized use.
- Disable unnecessary ports and services to limit access to medical devices.
While not required, these guidelines are highly recommended to ensure the safety and protection of medical devices and SaMDs. Following these guidelines will significantly reduce the risk of security attacks and breaches, ensuring the protection of sensitive patient information.
Beyond following these guidelines, there are several additional practices you can implement to better ensure device security. Building in security from the early stages of medical device design is key – ensuring that security is robust and thorough. It is important to note that no one security solution will best suit all devices. For this reason, it is essential to find the solution that best meets the unique needs of your organization and its devices.
Secure Solutions
Ensuring the security of your medical devices is a critical and necessary task. Your organization’s reputation and your integrity as a healthcare provider are dependent on your ability to protect sensitive patient medical information. As a result, your medical devices must have the utmost security, avoiding cyberattacks and breaches while performing efficiently. To achieve such a high and reliable level of protection, here are some best practices to follow:
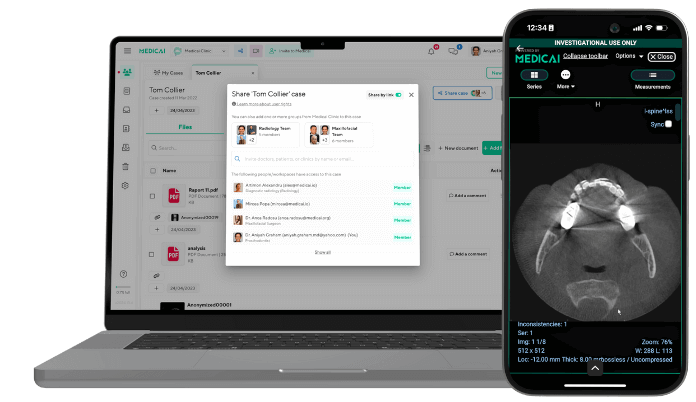
- Manage access and authorization. The most common causes for data breaches revolve around unauthorized users gaining access to an organization’s devices. But, by binding authentication to a corporate authentication system, this risk can be mitigated. This system, also known as healthcare MDM, will ensure that access is granted only to authorized users – for medical devices, this would be only healthcare providers and patients. Beyond this, monitoring for irregular activity and logins is crucial to identifying attack attempts. Password management is also instrumental in managing access, so passwords should be changed from the default and set as long, secure passwords specific to each individual.
- Protect endpoints. Medical devices require connections to various endpoints, such as MRI machines and the workstations they connect to. As a result, medical devices require more endpoints than typical devices, and the more endpoints a device has, the more opportunities there are for breaches. As these endpoints are necessary, they cannot be reduced. Instead, it is important to choose a medical device that directly supports antivirus software or requires additional integrity verifications.
- Asset management. Another beneficial practice for protecting medical devices is maintaining an IT asset inventory template, which helps you keep track of maintenance schedules and inventory, and supports decisions regarding replacements and vulnerabilities.
The security of your medical devices is a critical concern of healthcare providers. It is your responsibility to protect the information of both your organization and patients, and this starts with your medical devices. While guidelines are in place to ensure security, it is up to you to choose medical devices that you can trust and manage.
Obtaining a secure and up-to-date device with private access to data is critical, ensuring that you and your patients do not have to worry about compromised data or storage and platform updates. With the right technology and tools, you can ensure that your medical device is as secure as possible – ensuring the integrity of your practice.
Interested in learning more about telehealth? Contact one of our team members!
Related Articles
Lets get in touch!
Learn more about how Medicai can help you strengthen your practice and improve your patients’ experience. Ready to start your Journey?
Book A Free Demo